KYC in crypto is the process of verifying a user’s identity before access or continued use, aimed at aligning with regulatory expectations and reducing risk. It affects exchanges, wallets, and DeFi by shaping data sharing, onboarding, and ongoing AML controls. The balance between privacy and safeguards drives data minimization and auditable governance. Users face structured onboarding, consent-based checks, and regulator-aligned practices, creating a governance framework that weighs autonomy against security. The stakes point to a consequential, evolving landscape that warrants closer examination.
What KYC Is in Crypto and Why It Matters
KYC, or Know Your Customer, is the process by which crypto entities verify the identities and credibility of their users before allowing access to services. The practice alters risk exposure, shaping compliance pathways and operational practices. It highlights privacy tradeoffs and regulatory shape shifting, as firms balance safeguarding funds with user autonomy, while authorities pursue transparent, enforceable standards shaping future industry norms.
Where KYC Shows Up: Exchanges, Wallets, and Defi
Where does KYC legally and practically appear in the crypto landscape, and what are the concrete touchpoints across exchanges, wallets, and decentralized finance?
KYC implications shape on ramps and AML considerations, with regulatory geography dictating how data sharing and identity proofing occur.
Exchange vs wallet distinctions matter; privacy tradeoffs persist while on ramp solutions navigate evolving compliance and risk.
See also: Education Technology Trends
Balancing Privacy, Security, and Compliance
As KYC considerations shape the governance of exchanges, wallets, and decentralized finance, balancing privacy, security, and compliance becomes a practical imperative.
This posture recognizes privacy tradeoffs alongside robust controls; defenders seek proportional data collection and rigorous safeguards.
Regulation guides due diligence while preserving user autonomy.
Data minimization supports risk reduction, but requires clear scope, auditable processes, and transparent enforcement to sustain trustworthy ecosystems.
Practical Steps for Users: Onboarding, Verification, and Ongoing Checks
Practical steps for users in onboarding, verification, and ongoing checks emphasize a structured, regulator-aligned approach to access and maintain crypto services.
The process prioritizes transparent identity validation, risk-based monitoring, and ongoing compliance reviews, while acknowledging privacy tradeoffs.
Users balance convenience with safeguards, ensuring robust data minimization, auditable records, and clear consent, supporting compliant, freedom-minded participation through informed, deliberate user onboarding.
Frequently Asked Questions
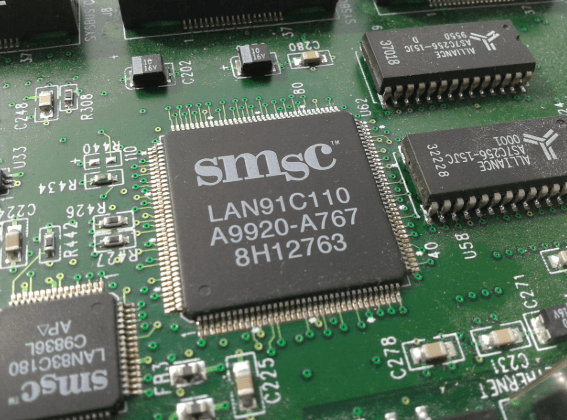
How Is KYC Data Protected Against Breaches in Crypto Platforms?
The article states data minimization limits collected information, encryption at rest protects stored data, governance and audits enforce accountability, and breach notification requirements ensure timely disclosure; regulatory emphasis guides risk-aware practices for platforms seeking user freedom.
Can KYC Affect Cross-Border Crypto Transfers and Reporting?
Like a compass under pressure, KYC impact on Cross border transfers shapes compliance risk. It can constrain timing, impose reporting duties, and influence jurisdictional transparency; regulators scrutinize transfers, demanding accurate KYC data to align with global reporting standards.
What Are the Costs Associated With KYC Compliance for Users?
Costs vary but center on verification fees, data security investments, and ongoing monitoring. The cost implications touch user onboarding smoothness, potential throttling, and compliance overhead. Regulators stress transparency, while risk-aware platforms balance freedom with auditable, regulated processes.
How Do Privacy Coins Fit Into Kyc-Regulated Environments?
Privacy coin usage intersects tightly with regulatory compliance, as authorities seek traceability. The analysis notes risks: non-compliance penalties, potential bans, and evolving frameworks. Stakeholders prioritize privacy features while ensuring adherence, balancing freedom with enforceable, risk-aware oversight.
Are There Alternatives to KYC for Onboarding New Users?
Access controls and pseudonymity limits shape onboarding alternatives; the path exists with risk-aware frameworks. The system, like a cautious lighthouse, guides compliant innovation, weighing privacy aspirations against regulation, while exploring zero-knowledge proofs, verified credentials, and behavior-based trust signals.
Conclusion
KYC in crypto serves as a regulatory fulcrum, balancing access with accountability. In practice, roughly 60–80% of centralized platforms now require verifiable identity, shaping onboarding and ongoing monitoring. The tight coupling of data minimization with auditable controls remains essential lest privacy erode under intensified oversight. A risk-aware, regulation-focused lens highlights that robust verification, consent, and transparent governance are not optional but foundational to trustworthy ecosystems where compliance does not stifle innovation.