Embedded systems are specialized computers embedded in everyday devices to run real-time tasks. They control sensors, actuators, and interfaces with strict timing and low power. Chips manage data locally, reduce latency, and extend battery life. Reliability and security are core concerns as devices become more autonomous. The practicality of edge processing shapes energy use and resilience in homes and gadgets. The next question is how these constraints scale with smarter ecosystems and user privacy.
What Are Embedded Systems in Everyday Devices
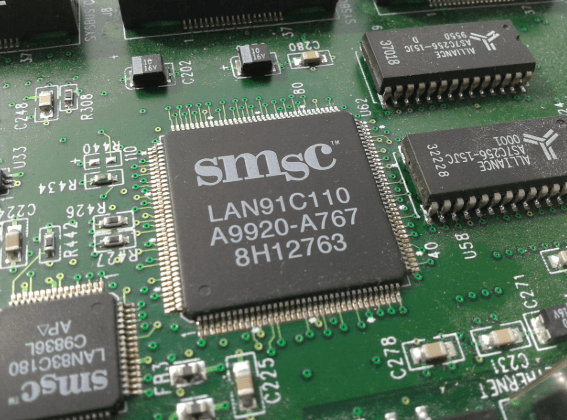
Embedded systems are specialized computers integrated into everyday devices to perform dedicated tasks with real-time constraints. They operate discreetly, controlling sensors, actuators, and interfaces without user intervention. This hardware-centric approach emphasizes deterministic timing, low power, and compact form factors.
Key considerations include reliability, resource limits, and security considerations, ensuring robust operation within appliance ecosystems and safeguarding privacy while preserving user freedom.
How Embedded Chips Drive Daily Convenience
Smart chips embedded in everyday devices streamline routines by handling sensing, processing, and actuation at the hardware edge. They enable responsive control, autonomous adjustment, and reduced latency, contributing to daily convenience.
Embedded chips power smarter homes while preserving reliability. Security evaluation remains essential as capabilities expand, ensuring robustness without compromising performance.
Hardware-focused design optimizes energy use, maintenance, and overall system resilience for freedom-loving users.
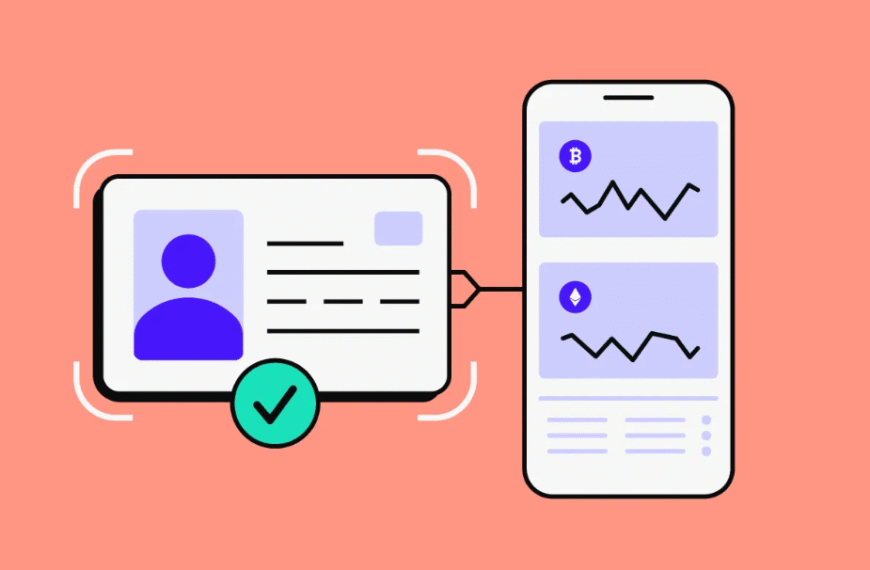
How to Evaluate Security in Common Devices
Security evaluation in common devices focuses on practical, hardware-grounded methods to verify resilience against real-world threats. Evaluators prioritize repeatable tests that stress interfaces, power, and firmware boundaries without relying on cloud assumptions. Security testing procedures emphasize tamper resistance, deterministic results, and reproducibility. Attention to supply chain integrity ensures components remain uncompromised from kit to deployment, reducing latent risk across ecosystems.
The Future: From Predictive Interactions to Smarter Homes
Predictive interactions will redefine the household by coordinating devices through edge-enabled reasoning and low-power sensors, enabling anticipatory control without reliance on cloud latency.
The future centers on predictive interfaces that orchestrate lighting, climate, and appliances with minimal user input.
Ambient intelligence emerges as a hardware-aware paradigm, optimizing energy use and responsiveness while preserving autonomy, privacy, and straightforward, freedom-focused installation and maintenance.
See also: Education Technology Trends
Frequently Asked Questions
How Do Embedded Systems Differ From General-Purpose Processors?
Embedded systems differ from general purpose processors in specialization and optimization; differentiation centers on targeted tasks, constrained resources, and real-time performance, whereas general purpose processors emphasize flexibility. This affects performance, power, and cost for hardware-focused applications.
Can Embedded Devices Be Repaired or Upgraded After Purchase?
Repair viability and upgrade paths vary by device: some embedded devices offer limited, manufacturer-supported service options, modular hardware, or firmware updates; others are sealed, media-only, or end-of-life. Freedom-seeking users should plan reliability and compatibility.
Do Embedded Systems Collect Data Anonymously or Personally Identify Users?
Data privacy varies by device; some collect basic telemetry, but anonymization attempts to strip user identifiers. An anecdote: a smart thermostat treats usage like data points, never names. Overall, data collection occurs with safeguards and optional opt-outs.
What Is the Typical Lifespan of an Embedded Device’s Firmware?
Firmware longevity varies but often spans 5–10 years in consumer devices, influenced by update cadence, security implications, and lifecycle management. It emphasizes practical maintenance, hardware constraints, and a freedom-minded approach to ongoing compatibility and resilience.
How Do Devices Handle Firmware Updates Securely Over the Air?
Secure OTA updates rely on firmware signing to verify integrity before installation, followed by encrypted transmission, robust rollback, and fail-safe recovery; hardware pins, trusted boot, and dual-image schemes ensure resilience for freedom-loving devices.
Conclusion
Embedded systems power everyday devices from thermostats to wearable sensors, delivering real-time control with predictable timing, low power, and compact form factors. Hardware-centric design choices—MCUs, SoCs, and secure boot—sonically shape reliability and privacy. A notable stat: approximately 90% of consumer IoT devices rely on energy-efficient microcontrollers for routine tasks, making power budgets and thermal limits critical. Practical security hinges on hardware-backed keys and firmware integrity. The trend points to smarter homes via edge processing and autonomous, resilient operation.